We are influencers and brand affiliates. This post contains affiliate links, most which go to Amazon and are Geo-Affiliate links to nearest Amazon store.
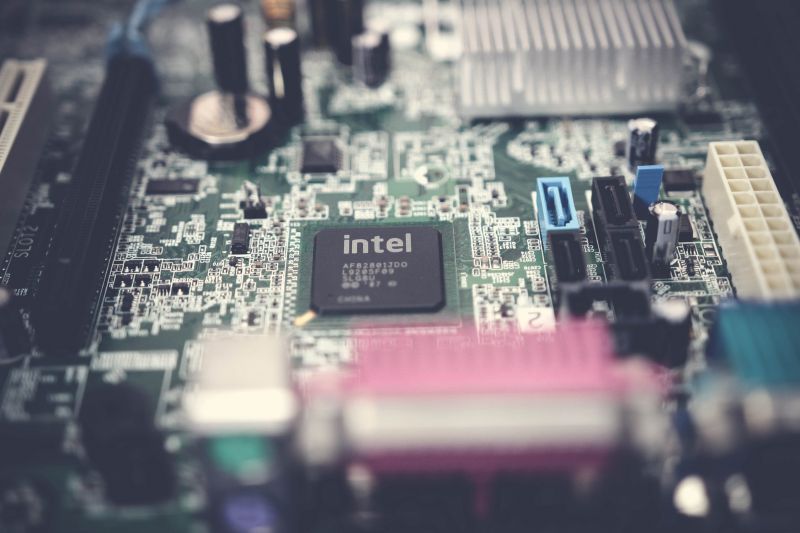
In 2018, January, the InfoSec community was stunned with the news about Intel security threat affected entire generations with the vulnerabilities of the meltdown and Spectre. It affects the entire generations of Intel at a large. In May, 2019, it has been found by the academics that there is also a side-channel attack that affects Intel process. With this attack the attackers are utilizing set of vulnerable data inside of your Intel CPU and retrieving data by using set of vulnerabilities. This attack is named as Zombieload and mostly similar to the Spectre, Meltdown and Forshadow side-channel hits that come out. Where Apple has already comes out with a new updates to secure the data from this vulnerabilities with its MacOS 10.14.5 update.
As reported by TechCrunch, security scientific study has discovered what they’re calling the latest class of vulnerabilities in Intel chips time for 2011 and doubles against virtual machines. As described by CPU fail, here’s the attack works:
“The ZombieLoad attack resurrects your private browsing-history and other sensitive data. It allows leaking information from other applications, the operating system, virtual machines in the cloud and trusted execution environments.”
As while using other three, the Zombieload flaw is exploited by abusing the speculative execution process. Speculative execution is undoubtedly an optimization technique where a pc system performs some task that is probably not needed. Work is carried out prior to it being known whether it is really needed, in an attempt to prevent a delay that have to be suffered by executing it after it is famous that it must be needed. If perhaps the repair hasn’t been needed, naturally, most changes created by the repair are reverted as well as outcomes are ignored. The academics who discovered the flaw published their findings in a academic paper titled, “ZombieLoad: Cross-Privilege-Boundary Data Sampling”, where previous to publishing the academics showcased spent higher than a year punching holes through the many pieces of the speculative execution process. What they have to discover was an episode method which allowed for your leaking of internet data from your target CPU’s buffer zones and data processing operations.As a company owner, its imperative to invest amount of time in teaching your team about basic cyber Security Best Practices – and through this effort, you will see the advantages spill over into your business. Let’s review seven personal security best practices to show your team today.
The modern vulnerabilities are constructed into Intel hardware and go past various names. ZombieLoad, Fallout, or RIDL tend to be the catchy ones; the harder technical name is Micro architectural Data Sampling (MDS). Before we have with it more, then you would you like purchasing it.
How you will should be affected by MDS is most likely everything that you anticipate: if you wish to updateOS in this system when it asks one to and likewise ensure that your browser is up to date — either could be a vector for these new attacks. Only devices running on Intel chips are affected (though it’s each between 2011 the release quite new chips), so iOS devices and almost all Android products are safe. And it needs to be said there is been no reported exploits gaining from these vulnerabilities on the wild.
There are actually major obstacles to exploiting Zombieload from the untamed, which forms element of the good thing is in conjunction with Intel’s readiness to combat the flaw if exploited by the malicious attacker. Intel noticed that exploiting this vulnerability, just like other side-channel attacks, away from a laboratory is quite complex then when one considers the countless other thoroughly tested methods on the market to hackers this cuts down the possibility of it been used from the wild into a major extent.
Most Mac OS users can ensure they are updated to Mojave 10.14.5 which contains general remediation for the Zombieload, but to be 100% sure to prevent this vulnerability you have to disable hyperthreading altogether which may be overkill but just putting it out there.
In Mac OS, you can go to the Utilities screen, pull down the Utilities menu in the menu bar and select terminal. Type the following command in the terminal: nvram boot-args=”cwae=2″ and this will disable hyperthreading on your Mac OS.
We are influencers and brand affiliates. This post contains affiliate links, most which go to Amazon and are Geo-Affiliate links to nearest Amazon store.
I am interested in all things technology, especially automation, robotics and tech that helps change how society will live in the future.